Malware Traffic Analysis Exercise - EGGNOG SOUP
This challenge is from MALWARE-TRAFFIC-ANALYSIS.NET. Download the PCAP ZIP yourself here. Check their about page for the password.
Scenario
LAN segment data:
- LAN segment range: 172.16.3.0/24 (172.16.3.0 through 172.16.3.255)
- Domain: eggnogsoup.com
- Domain controller: 172.16.3.2 - EggNogSoup-DC
- LAN segment gateway: 172.16.3.1
- LAN segment broadcast address: 172.16.3.255
Task
- How many hosts besides the Domain Controller at 172.16.3.2 are active on the network?
- 9 hosts
Filtered with ip.src == 172.16.3.0/24 and ip.src != 172.16.3.2 and counted.
- List the IP addresses for the hosts found when investigating the previous question.
- 172.16.3.109
- 172.16.3.110
- 172.16.3.111
- 172.16.3.112
- 172.16.3.114
- 172.16.3.122
- 172.16.3.133
- 172.16.3.188
- 172.16.3.189
- Which IP address represents a host running Ubuntu?
- 182.16.3.110
Filtered on http.user_agent contains Ubuntu.
- What type of host is using IP address 172.6.3.188?
- iPhone
Filtered on ip.addr == 172.16.3.188 and http and the User-Agent was Mozilla/5.0 (iPhone; CPU iPhone OS 12_1_1 like Mac OS X) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0 Mobile/15E148 Safari/604.1.
- Which IP address is mostly likely an Amazon Fire tablet?
- 172.16.3.109
Filtered on dns.qry.name contains amazon and found the device with that IP had a MAC address of AmazonTe_d2:5e:47 (b0:fc:0d:d2:5e:47).
- Which three IP addresses represent Windows hosts that connect to the domain controller at 172.16.3.2?
- 172.16.3.114 - GOODSON-WIN-PC$ - emelda.goodson
- 172.16.3.133 - VARNER-WIN-PC$ - conception.varner
- 172.16.3.189 - PALUMBO-WIN-PC$ - odell.palumbo
Filtered on ip.src == 172.16.3.0/24 and kerberos.CNameString with CNameString as a column.
- Which of the three Windows hosts shows indications of an infection with Emotet and IcedID banking Trojan (Bokbot)?
- 172.16.3.133
Per an image of the Emotet and IcedID traffic, I could check what looks similar.
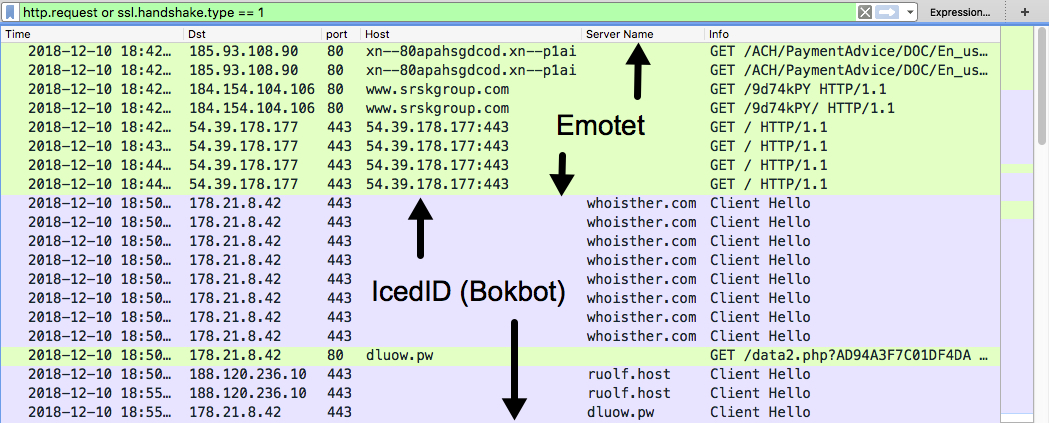
Filtering on ip.src == 172.16.3.133 and (http.request or ssl.handshake.type == 1), I see similar traffic and a GET request to a host on a .pw address for a /data2.php file.
- Which IP address is a host running Android 8.0.0?
- 172.16.3.111
I first tried filtering on http.user_agent contains Android to no results, but I found the answer after putting quotes around "Android".
- What is the brand and model of the phone running Android 8.0.0?
- moto e5 play, Motorola_91:a6:ed (bc:ff:eb:91:a6:ed)
Checking the Ethernet II and HTTP layers on packets from the previous filter, we get our model.
- What is the brand and type of device on 172.16.3.112?
- Samsung Galaxy Tab E Lite
Filtering on ip.addr == 172.16.3.112 and http, I grab the following info: Android 4.4.4; SM-T113 Build/KTU84P, SamsungE_99:41:07 (68:e7:c2:99:41:07). Googling SM-T113, I found the device to be a Samsung Galaxy Tab E Lite which lines up with the other info.